Based on Device Posture
The InstaSafe Zero Trust security framework verifies both users identify and device before enabling access to critical applications. Under the tenets of Zero Trust, only verified devices and users are granted access to assets, applications and systems. Device posture is a measurement of how secure and compliant the device is. By monitoring and enforcing device posture, organizations can prevent malicious devices from accessing sensitive information and critical applications.
InstaSafe ZTAA empowers administrators to ensure that only devices that comply with predefined security policies can access the enterprise applications from the agent.
Device posture attributes available in ZTAA
- Application
- Application Access Time
- AntiVirus Enabled Name
- AntiVirus Installed Name
- AntiVirus Updated Name
- Certificate Thumbprints
- Country Code
- Disk Serial Number
- Geolocatoin
- IP Address
- Mac Address
- Motherboard ID
- OS Build Version
- OS Family
- OS Major Version
- OS Minor Version
- System Domain Name
- System MacAddress
- System Serial number
- Windows Hotfixes
- UA Suffix
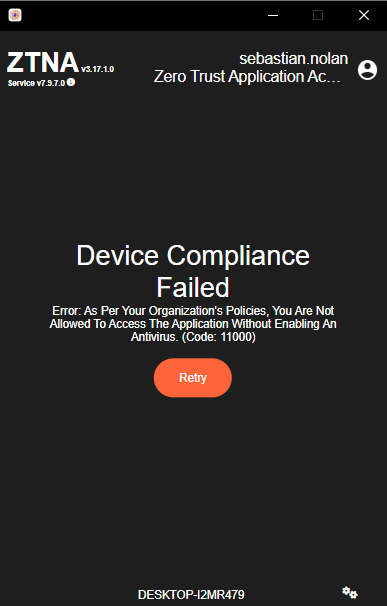
An organization has provisioned application access over the InstaSafe Zero Trust platform (ZTAA) and wants to enforce a device posture check that AntiVirus should be available in the end user devices before application access. A device compliance rule for AntiVirus check can be defined in the ZTAA platform. Any user trying to connect to the InstaSafe ZTNA agent for application access will be restricted from connecting to the agent if they do not have AntiVirus installed in their device and will be presented with a message as shown in the below screenshot.
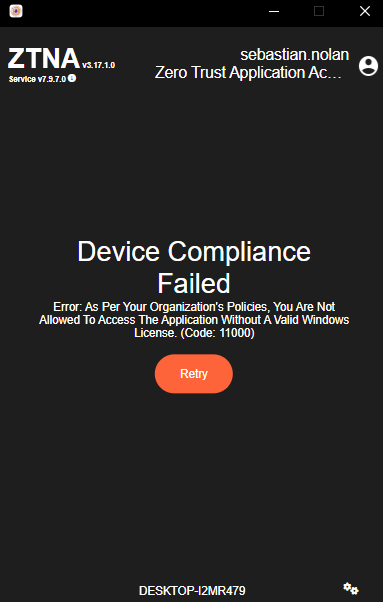
An organization has defined a device compliance rule for users to connect only from devices which has a Genuine Windows OS. Any user trying to connect to the InstaSafe ZTNA agent for application access will be restricted from connecting to the agent and will be presented with a message as shown in the below screenshot if their Windows machine does not have a genuine licensed OS.
Implementation of Device posture check in ZTAA is a two step process:
- Create a device posture profile dataset.
- Add the device posture profile dataset in Access Policy.
Create Device posture profile in ZTAA
To create a device posture profile dataset in the ZTAA console follow the below steps:
- Click on “Configuration” in the left menu.
- Navigate to the “Data Management” tab.
- Click on the “+” icon to create a new dataset.
- Select the device posture attribute available in the “Select Variable” dropdown.
- Enter the Dataset name and description click on “Add Dataset”.
- Search for the created Dataset and click on Edit.
- Click on the “Records” and add a record value.
Apply Device posture profile in Access Policy
To assign a device posture dataset to access policy perform the below steps:
- Click on “Access Policy” in the left menu.
- Search for the access policy to which you would like to add a device posture dataset.
- Select the Access Policy and click on Edit.
- Navigate to the “Manage Rules” tab.
- Click on the “+Rule” and select the device posture attribute.
- Select the device posture profile dataset and click on “Update Manage Rules”.
After the above configurations are performed, users when they login to the ZTAA agent will not have access to the applications to which they are granted access to if their device does not comply with the configured device posture profile.